Recently I open sourced a complete serverless web application which can be deployed on the IBM Cloud in less than 10 minutes. In this article I describe how users are authenticated via IBM App ID.
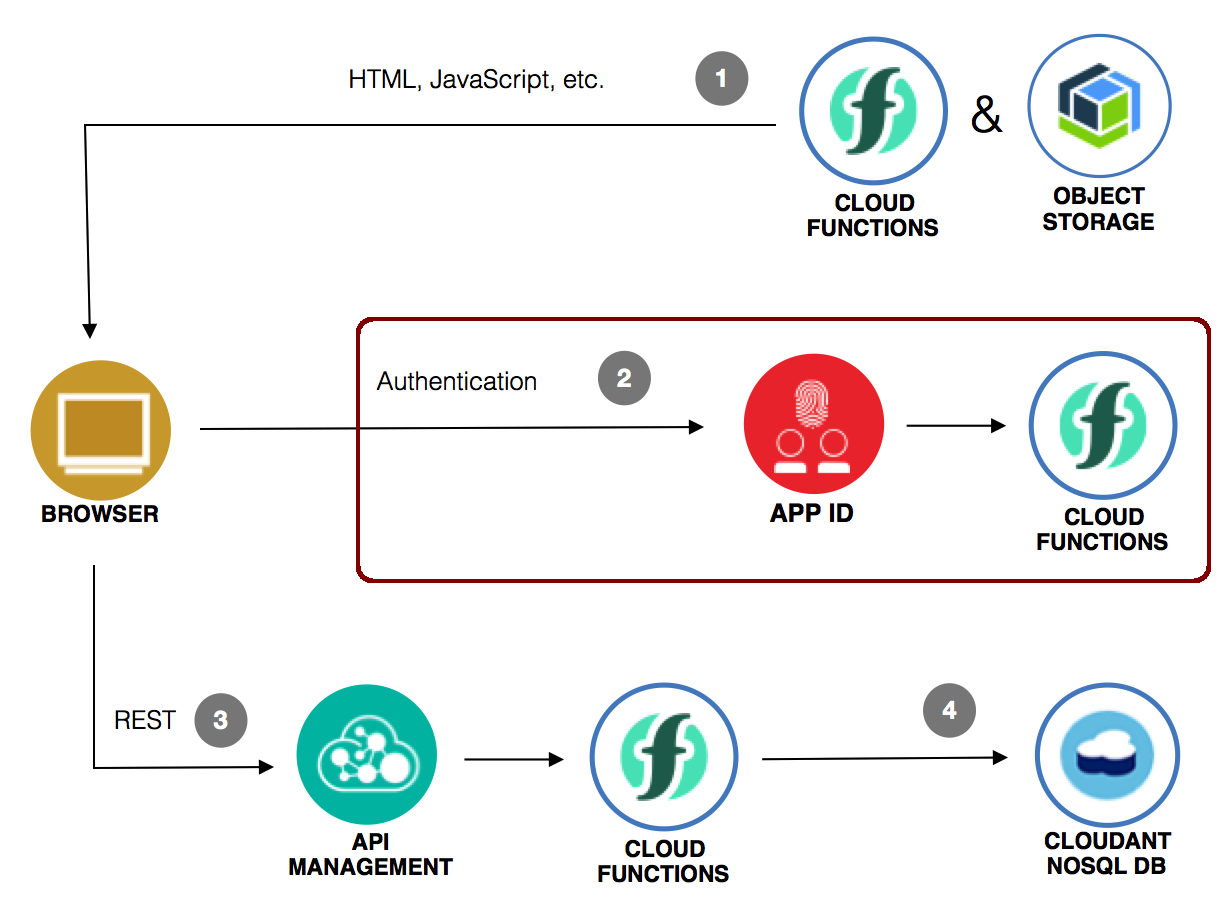
My sample describes how to host static resources on IBM Object Storage, how to authenticate users via IBM App ID, how to access IBM Cloudant from OpenWhisk functions and how to use API management. This diagram shows the main components. In this article I focus on the authentication flow.
Watch the 10 seconds video for a short demo of the OAuth dance.
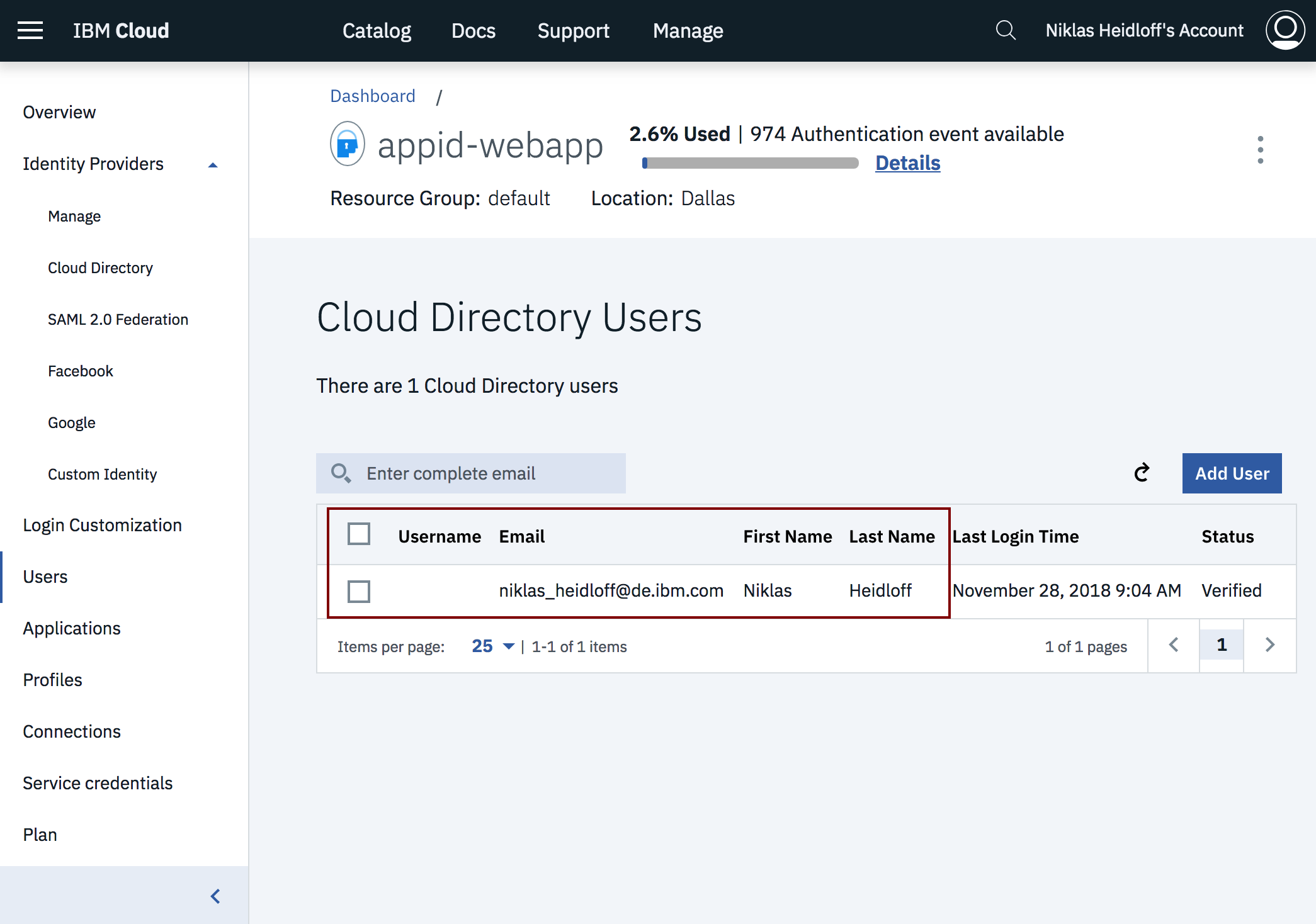
App ID helps developers to easily add authentication to their web and mobile apps with few lines of code. Several different identity providers are supported. For example for enterprise applications you can use your existing identity provider via SAML. To keep my sample as easily as possible I use a cloud directory with one test user:
App ID also comes with authentication pages for web applications which can easily be customized. This allows developers to focus on their business logic rather than having to write their own authentication pages and flows.
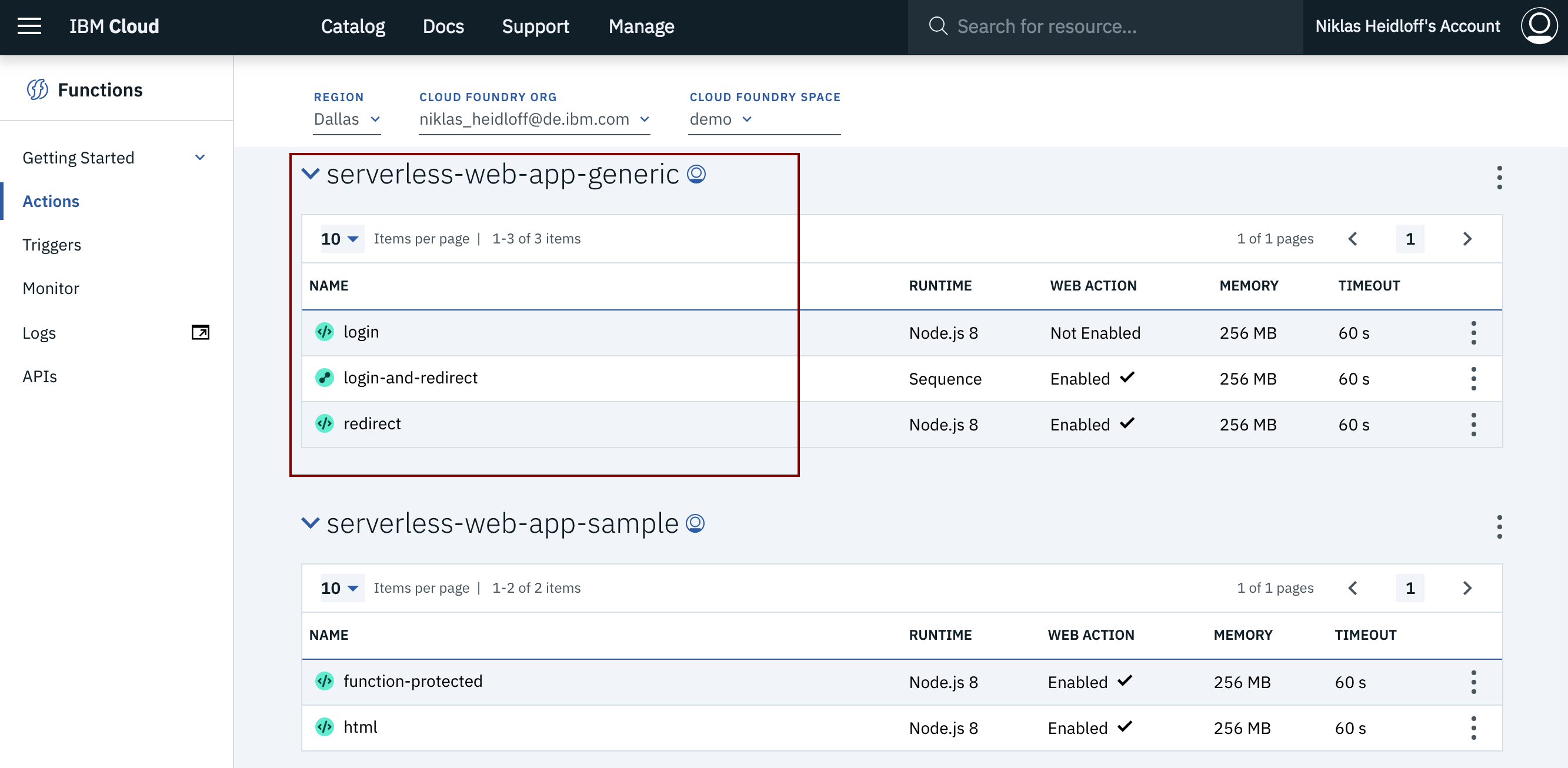
App ID can easily be used in server side code. In this case the client ID and client secret are stored on the server. For serverless applications, these credentials must not be stored in the client for security reasons. That’s why I’ve implemented OpenWhisk login functions which authenticate users via OAuth.
These two functions and the sequence are generic and can easily be used in other web applications hosted on the IBM Cloud. Read my previous article to understand how these functions and the sample Angular app invoke and execute the OAuth dance. When I wrote that article, the App ID cloud directory didn’t exist which is why I choose Google as identity provider.
If you want to try this functionality yourself, create an IBM Cloud lite account (free, no credit card required) and follow the steps outlined in my repo.
This article is part of a mini series. Check out the other articles and documentation: