At the beginning of this year the Single Sign On service in Bluemix was extended to support SAML as identity provider. This allows to leverage existing existing organization directories for authentication of users in the cloud.
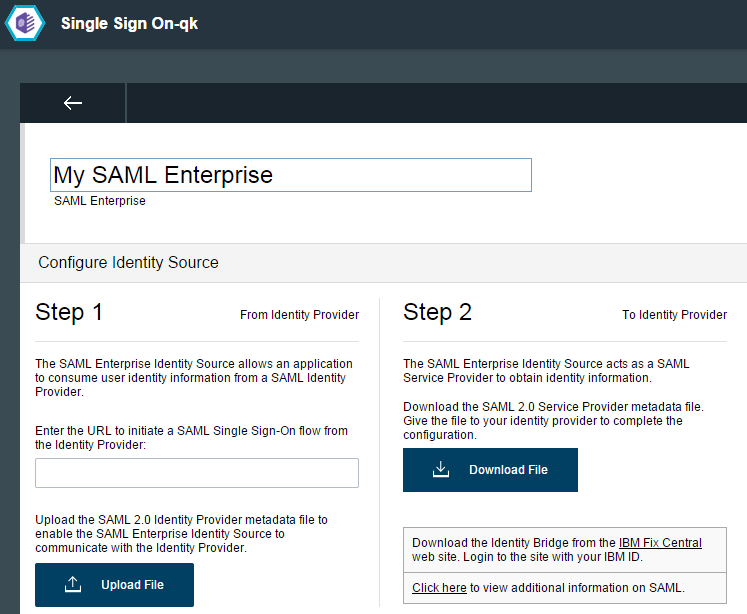
As described in the documentation “Security Assertion Markup Language (SAML) is an XML standard for exchanging single sign-on information between an identity provider who asserts the user identity and a service provider who consumes the user identity information. The SAML Enterprise Identity Source acts as a service provider. It allows an application to contact a separate identity provider to authenticate users and consume the returned user identity information.”
Last week IBM previewed a new XPages runtime on Bluemix to host applications based on IBM Domino in the cloud. In this context developers asked how to authenticate users against existing IBM Domino (LDAP) on premises directories. I had planned to try out a solution that should work but haven’t had the time to do so. Since I won’t have time to work on this anytime soon, I want to at least give some hints how this should work. But again, I haven’t tried it myself yet.
Since version 9 Domino can be used as service provider and can defer to identity providers for authentication. As identity providers you can use IBM Tivoli Federated Identity Manager (TFIM) and Microsoft Active Directory Federated Services (ADFS). As far as I understand it should be possible to use these providers in the SAML configuration for Bluemix above.
The Bluemix documentation also mentions an identity bridge component which can help to leverage LDAP enterprise directories: “The identity bridge extends the IBM Bluemix Single Sign On service to your enterprise by externalizing the SAML protocol as a method of authenticating users to an LDAP version 3 compliant directory in your enterprise. … The identity bridge is a separate component that is provided by the Bluemix Single Sign On service, for download to an on-premises environment. … The component can then be deployed to the appropriate on-premises location.”